inventory-sudoers
Installation
cfbs add inventory-sudoers
The sudo program allows a user to execute a command with elevated privileges.
It is a good idea to limit and monitor who has access to do this.
This module will check which users on a system can use sudo (sudoers) and report that as part of CFEngine Enterprise Inventory.
In Mission Portal, the CFEngine Enterprise UI, you can get reports of all users with sudo access across all machines in your infrastructure:
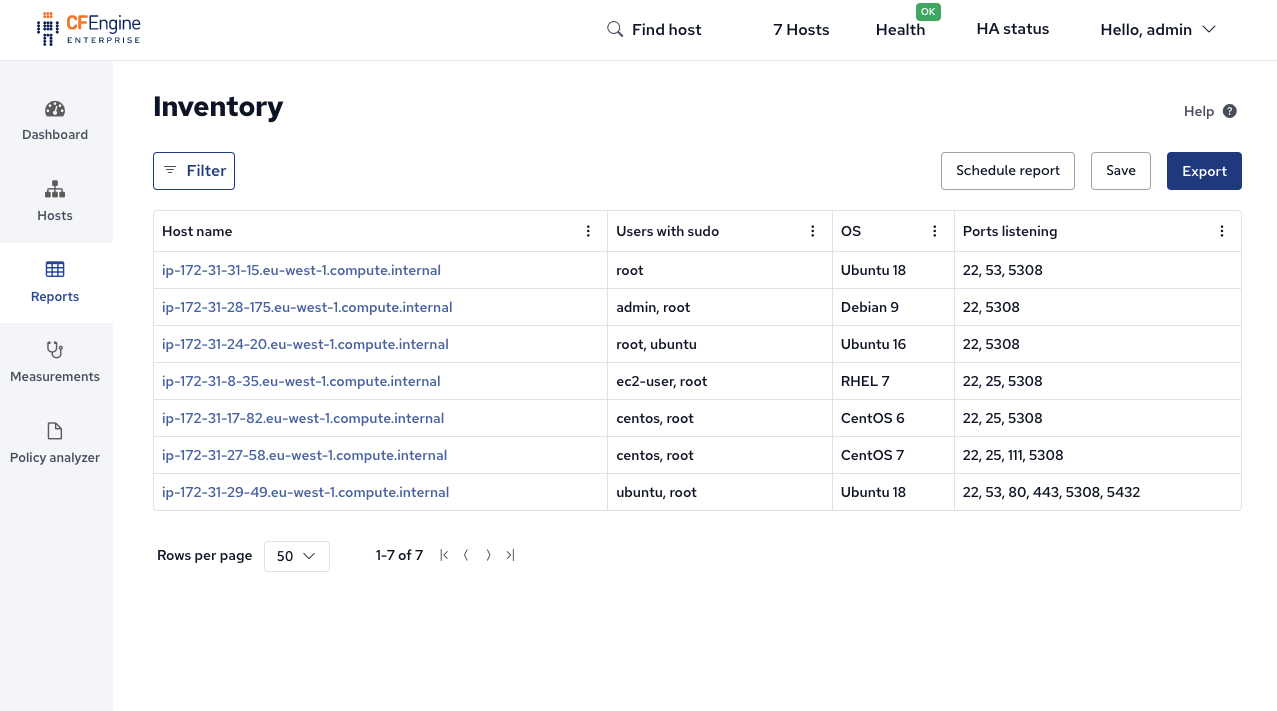
(To see this, go to Reports -> Inventory -> Click the 3 dots at the top of a column -> Insert Column -> Users with sudo)
You can also see the list of sudoers for a single machine from the command line:
$ sudo cf-agent --show-evaluated-vars -KI | grep "_inventory_sudoers.users"
nickanderson:_inventory_sudoers.users {"root","ubuntu"} source=promise
Recommendation: Review this list on a regular basis, and ensure all of the users really need sudo access.
Remove sudo access where possible by editing the /etc/sudoers file.
Requirements
- CFEngine version 3.18.0 or greater (in order to configure without modification)
Inventory
- Users with sudo
- List of users that have sudo access as determined by
sudo -l -U <USERNAME>
Variables
-
nickanderson:_inventory_sudoers_main._users_list_var (
String) - Defines the name of the variable expected to hold a set of users to evaluate for sudo access, defaults to
nickanderson:_inventory_sudoers_main._users -
nickanderson:_inventory_sudoers_main._users (
List) - The default variable to use when evaluating sudo access which defaults to the list of users from
/etc/passwd -
nickanderson:_inventory_sudoers_main._refresh_frequency_min (
Int) - How long to wait before clearing cache and re-evaluating which users have sudo access, by default
30
Examples
Set the list of users to check for sudo access
As of 3.18.0, Augments allows variables to be defined in a specific bundle by leveraging the variables key.
This Augments sets the list of users to check for sudo access:
{
"variables": {
"nickanderson:_inventory_sudoers_main._users": [ "luke.skywalker",
"minch.yoda",
"obiwan.kenobi" ]
}
}Use with cfbs
The cfbs tooling allows you to manage a CFEngine policy set, and all its dependencies in an easy way.
If you've never used cfbs before, here are the steps to get started.
Install dependencies
Before installing and running cfbs, you need pip3 (and Python 3.5 or newer), and autotools (autoreconf, automake).
If you don't have these tools already, there are many ways to install them, here are some suggestions for Ubuntu, CentOS and macOS.
Ubuntu:
$ sudo apt-get install -y python3 python3-pip automakeCentOS:
$ sudo yum install -y python3 python3-pip automakemacOS:
brew install python3 automakeInstall tooling
$ sudo pip3 install --upgrade pip
$ sudo pip3 install cfbs cf-remote
(cf-remote is optional, only needed for deploying to remote machines).
Create a project
$ mkdir my-policy-set
$ cd my-policy-set
$ cfbs initAdd modules
$ cfbs add masterfiles
$ cfbs add inventory-sudoersBuild
$ cfbs buildDeploy
If you are running CFEngine locally:
$ sudo cfbs buildIf CFEngine is running on a remote hub:
$ cf-remote deploy --hub username@1.2.3.4 out/masterfiles.tgz
(Replace username@1.2.3.4 with the username / IP you use to SSH to your hub).
Dependencies
This module has no dependencies